China’s Cybersecurity and Data Compliance:
What Foreign Businesses Need to Know
📅 19/03/2025
China’s data protection and cybersecurity laws have become increasingly significant for foreign businesses due to their evolving complexity and stricter enforcement, and non-compliance can lead to hefty fines, suspension of operations and criminal liabilities.
China has been developing a robust legal framework for data protection and cybersecurity since 2017, when the country enacted its first comprehensive legislation regulating cyber networks – the Cybersecurity Law (CSL). The Data Security Law (DSL) and the Personal Information Protection Law (PIPL), both effective in 2021, are among the other key laws shaping the national framework.
Within the legal framework, over 100 implementation rules and standards have been introduced at national level, continuously advancing and refining the regulatory regime. These rapidly evolving laws and regulations cover a wide range of sectors and entities, and pose significant compliance challenges for foreign companies operating in China.
Foreign businesses need to have a clear understanding of the legal framework, regulatory approach, potential extraterritorial effects, and the consequence of non-compliance, as this understanding allows them to proactively assess their position and implement necessary compliance measures.
The structure of the regulatory regime
The Cybersecurity Law establishes the fundamental principles for ensuring cyber operational security and information security. Under this law, “cyber operators” are responsible for safeguarding cybersecurity in their operations. The obligations include but are not limited to compliance with the Multi-Level Protection Scheme (MLPS) for cybersecurity; ensuring the security of network infrastructure; ensuring the security of cyber products and services; and protecting personal information. The term cyber operator broadly includes network owners, administrators, and service providers. Businesses falling within this category must assess and fulfil their cybersecurity obligations. Notably, this definition extends beyond traditional technology companies or providers of network-related products and services; it also covers entities that rely on networks in their operations, such as hotels, healthcare providers, and other enterprises.
The regulatory burden is even higher for operators of critical information infrastructure (CIIOs), which are responsible for IT infrastructure in key industries and sectors such as energy, transportation, finance, public services, and e-government systems. The CIIOs have to comply with stricter security measures, management responsibilities, and assessment requirements. This is because if these critical IT systems are damaged, disabled, or subject to data breaches, there would be sever impact on national security, economic stability, public welfare and the overall public interest.
For network operators and businesses that collect, process, or handle network data and personal information during their operations, their compliance obligations span the entire data lifecycle, including data collection, storage, usage, processing, transfer, provision, and disclosure.
The flowchart below outlines the key laws and regulations governing cyber operational security and cyber information security.
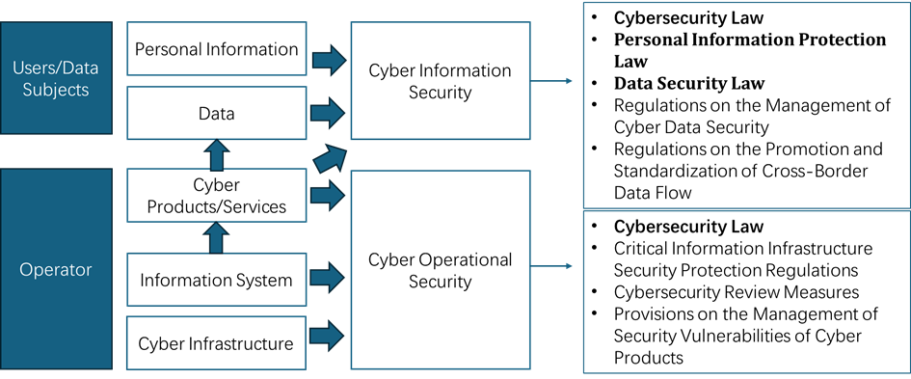
In addition to these overarching regulations, specific industries such as the automotive, pharmaceutical, financial, and app sectors have introduced their own specialised cybersecurity and data compliance requirements.
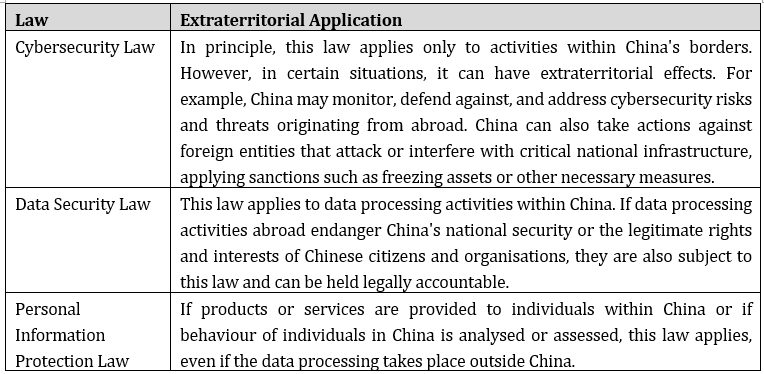
Extraterritorial Application
Many rules of China’s data protection and cybersecurity regime have extraterritorial effects. This means they can apply to activities outside of China under certain conditions. Companies that are working with China, have commercial interests there, or are producing goods in China or distributing to or from the country, are likely to be affected.
The table below provides a brief summary of the extraterritorial implications of the three main laws.
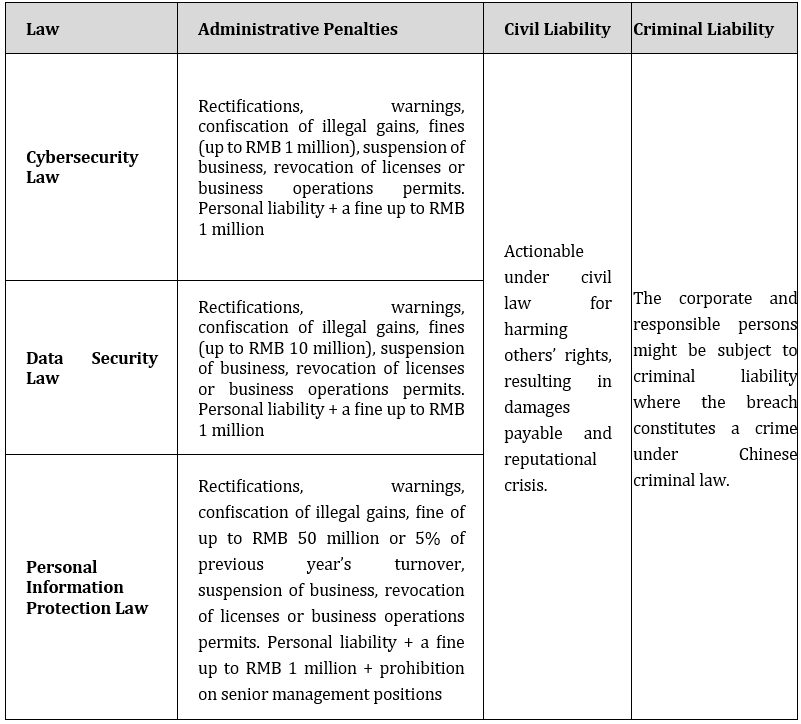
Consequences of non-compliance
Non-compliance with China's data protection and cybersecurity laws can lead to severe consequences for organisations. Companies breaching the laws could face financial penalties, operational disruptions, reputational damage, civil and criminal litigation risks, and cross-border implications.
Main regulators
The main regulators under China’s data protection and cybersecurity regulatory regime include:
• Cyberspace Administration of China (CAC), also known as Office of the Central Cyberspace Affairs, which is the leading regulator overseeing cybersecurity and data protection;
• The Ministry of Public Security, which is responsible for enforcing cybersecurity measures, investigating cybercrimes and ensuring the protection of critical information infrastructure;
• State Administration for Market Regulation, which is in charge of enforcing consumer protection law, including those related to personal information protection;
• and sector-specific regulators, such as the securities regulator, the central bank, and the Ministry of Industry and Information Technology.
Steps to take
It is vital for foreign companies operating in or dealing with China to carry out thorough risk assessments and ensure compliance with the intricate legal and regulatory requirements in China, especially given their extraterritorial effects.
Here are some key steps foreign companies should take:
• Conduct compliance risk assessments to evaluate cybersecurity and data protection obligations applicable to business operations.
• Form a clear strategy to minimise the risks in relation to penalties, including possible hefty criminal liability for relevant company executives and officeholders.
• Seek professional advice on governance, compliance, procedures, cross-jurisdictional emergency, contingency plans, internal roles, and responsibilities.
• Implement data categorisation to classify data into different categories based on its sensitivity, importance and different level of regulatory and compliance requirements under Chinese law.
• Carry out cross-border data transfer and data compliance audit to comply with mandatory requirements in specific commercial circumstances.
This article is part of a practical guide series by Thornhill Legal to help foreign companies navigate China's intricate cybersecurity and data compliance regulations. The series also explores topics such as:
• Data Export from China
• Managing Employee Data in China
• Personal Information Compliance Audit
• Artificial Intelligence Generated Content (AIGC)
Key contacts / Authors
Yuhua YANG: yuhua.yang@thornhill-legal.com
April XIAO: april.xiao@thornhill-legal.com
Rhea YU: rhea.yu@thornhill-legal.com
Standard Terms of Business | Legal Notice | Privacy Policy | Terms & Conditions | Our Compliants Policy | Cookies Policy
© Copyright Thornhill Legal Ltd. All rights reserved.
We need your consent to load the translations
We use a third-party service to translate the website content that may collect data about your activity. Please review the details in the privacy policy and accept the service to view the translations.
